PennKey logins allow any previously-allowed user within SAS, or the university, the ability to access a public computer without having a local user account on that computer or a domain user account. All Macs in the SAS Central Pool Classrooms use this type of authentication.
Mac OS X uses PennGroups and kerberos to facilitate PennKey authentication. The following procedure works on OS X versions 10.8.4 – 10.14.6
Requirements: access to PennNet, PennGroups LDAP account (ask jasonrw), administrative access to the target Mac OS X 10.8.4 – 10.14.6
UPDATE (1/31/21): Apple introduced lots of changes with macOS 10.15 “Catalina.” Some of these differences broke the manner in which we have traditionally configured PennKey authentication. The good news is that 10.13, 10.14 Macs, configured for PennKey authentication and upgraded to 10.15 continue to permit PennKey logins. The Bigfix fixlet, which configures PennKey authentication no longer works.
The same can be said for macOS 11 (10.16?) “Big Sur.” Upgraded PennKey Macs do continue to permit PennKey logins. The rub is that none of the configuration profiles installed onto macOS are accessible by PennKey users. Admin users are fine, but unprivileged PennKey users will get a barrage of admin authentication prompts which never end. Even if an admin username/password are provided, the prompts keep coming. At this point, Big Sur is not viable for use with PennKey authentication.
UPDATE (2/15/18): The EMS team has created an IEM (BigFix) fixlet which will do all of the following on any relevant Mac. As much fun as it has been going through motions of setting up this type of access manually, it is no longer required.
Note: This process modifies how OS X authenticates users each time they log in. Mistakes here could render the Mac unable to authenticate any user. It would not be a bad idea to make a backup of the target Mac prior to beginning this configuration procedure. I use Disk Utility for this purpose.
The first part of this involves modifying three configuration files that help set up kerberos authentication.
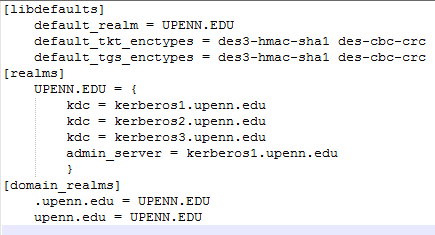
The FIRST part is to create a “krb5.conf” file on the target system, or download one from here or open up the terminal and create a new file, called krb5.conf, under /etc (sudo nano /etc/krb5.conf). Edit the file to match what is listed below.
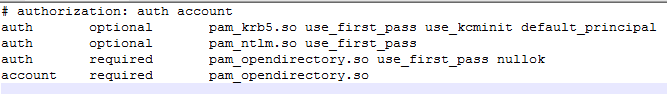
The SECOND part is to setup the Mac OS X login window for kerberos authentication by modifying the preexisting “/etc/pam.d/authorization” file.
Again, from the Terminal and type sudo nano /etc/pam.d/authorization. Then, navigate to the first auth optional section and add the value“default_principal” to the end of the line, as shown below.
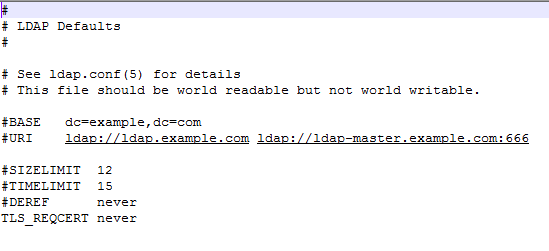
THIRD. Configure Open LDAP to ignore certificates by editing the preexisting “/etc/openldap/ldap.conf” file. From the Terminal, enter the command sudo nano /etc/openldap/ldap.conf. You will need to edit the line that reads TLS_REQCERT DEMAND and change DEMAND to never as shown below.
FOURTH, configure Directory Access. This is by far the most tricky part of the whole procedure. Steps have to be performed exactly as indicated or else PennKey authentication WILL NOT work.
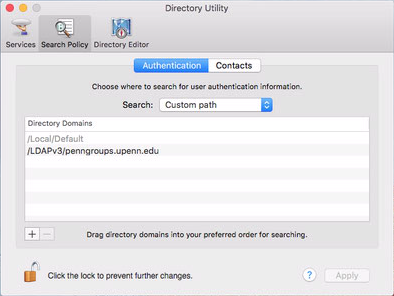
Open the Directory utility, while logged-in as an admin user. Apple buries the Directory Utility in the Users applet in System Preferences.
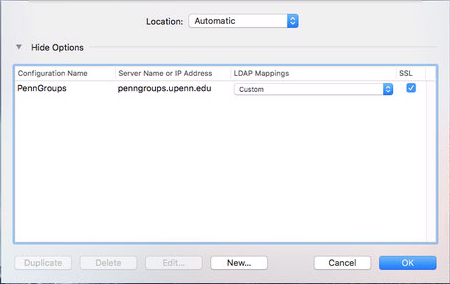
Select LDAPv3 and then click the edit box below and a new window will appear. Click on New then click Manual then click Edit. Under the Connections tab, enter the information as shown in the box below.
- name the configuration PennGroups
- enter the server name penngroups.upenn.edu
- check the box Encrypt using SSL
Leave the rest at their defaults and then click on Search and Mappings tab at the top.
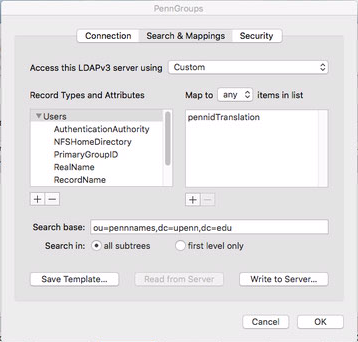
- In the drop down box next to Access this LDAPv3 server… select Custom
- Select the Default Attribute Types, then click Add, then select Record Types and highlight Users
- Select the Users record type you just added and click the Add button that is located under the right pane (Map to ‘any’ items in list)
- Add the value pennidTranslation and
- Set the Search base for the Users record type: ou=pennnames,dc=upenn,dc=edu and select Search in all subtrees as shown below.
Now comes the fun part, adding the attributes for the Users record type. They all have to be added and in the following order. The order must be correct and exact, or else none of this will work.
- AuthenticationAuthority
- NFSHomeDirectory
- PrimaryGroupID
- RealName
- RecordName
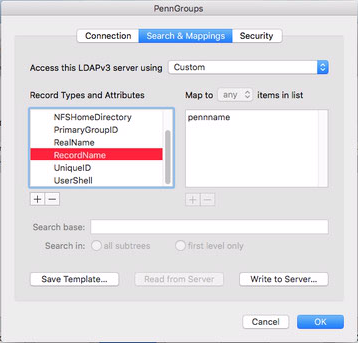
- UniqueID
- UserShell
- AuthenticationAuthority = pennname
- NFSHomeDirectory = #/Users/$pennname$
- PrimaryGroupID = #20
- RealName = cn
- RecordName = pennname
- UniqueID = pennid
- UserShell = #/bin/bash
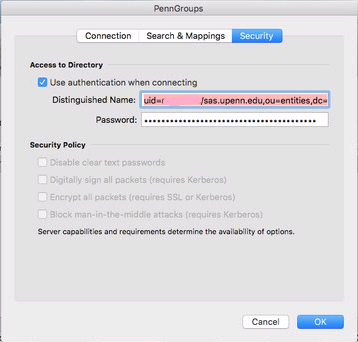
Almost done! Next, we have to configure directory authentication for the whole configuration. ISC would have had to provide the organization with a username and password for this part. Open the “Security” tab next to the “Search and Mappings” tab.
- Check the box to Use authentication when connecting
- Enter the Distinguished Name of the principal (service account) that has been setup (see the prerequisites) in the format uid=<principal>,ou=entities,dc=upenn,dc=edu
for example:
uid=mac-stuff/sas.upenn.edu,ou=entities,dc=upenn,dc=edu - And enter the password for that account, as shown below. OK out of the PennGroups settings dialogs until you are back at the Directory Utility window.
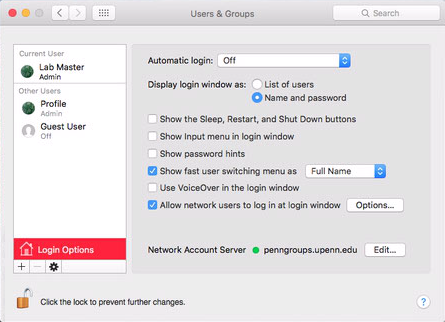
Change the log on window for OS X to not show a list of users, but just the username and password dialog boxes, or else you will not be able to log on with a PennKey. Go into System Preferences \ Users & Groups \ Select the “Login Options” button and select “Name and password” radio button under the “Display login windows as:” section.
sudo defaults write /Library/Preferences/com.apple.loginwindow LoginwindowText "Please log in with your PennKey username and password."